Table of Contents
- 1. Scope and Approach
- 2. Binary Analysis in Cutter
- 3. String Analysis
- 4. Finding the Flag Logic
- 5. Understanding the Vulnerability
- 6. Patching the Binary
- 7. Final Result
- 8. Conclusion
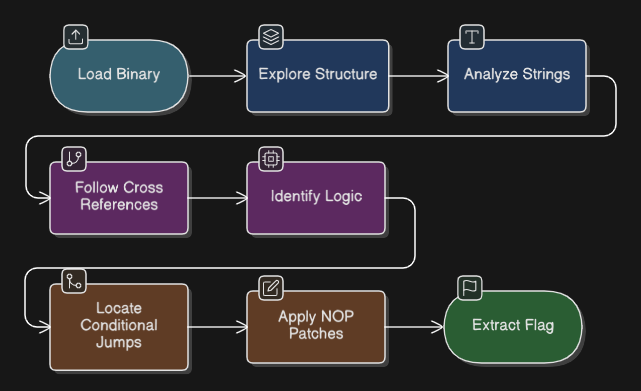
1. Scope and Approach {#scope}
In this task, I performed static analysis on a crackme executable using Cutter. I focused only on static analysis and did not use any unsafe execution methods. The goal was to understand how the program works internally, identify hidden functionality, and then modify the binary to bypass the checks and directly access the flag.
My approach was to first explore the structure of the program, then analyze strings, follow the execution flow, and finally apply patches to change the behavior of the program.
2. Binary Analysis in Cutter {#binary-analysis}
I started by opening the executable in Cutter and enabling auto-analysis. This allowed Cutter to analyze the binary and identify functions, strings, and code structure.
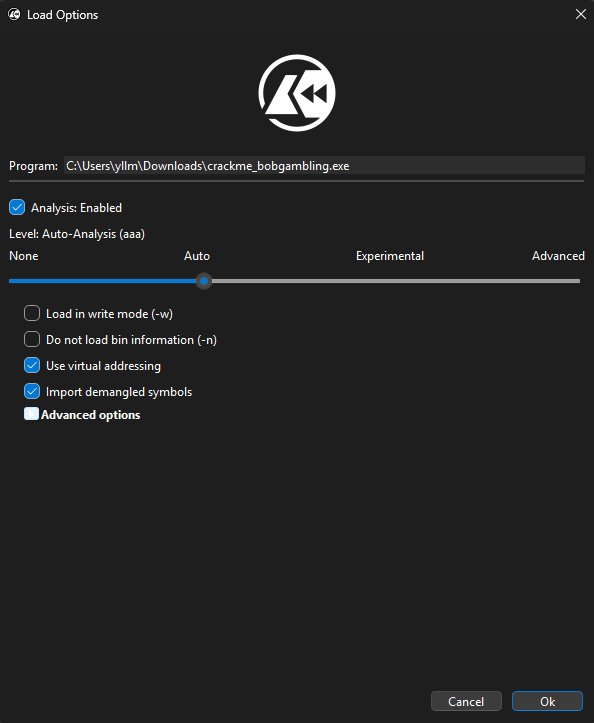
By doing this, I was able to see the disassembly, functions list, and references inside the program. This is important because it gives a full overview of how the program is organized and where important logic might be located.
3. String Analysis {#strings}
After loading the binary, I moved to the Strings section in Cutter.
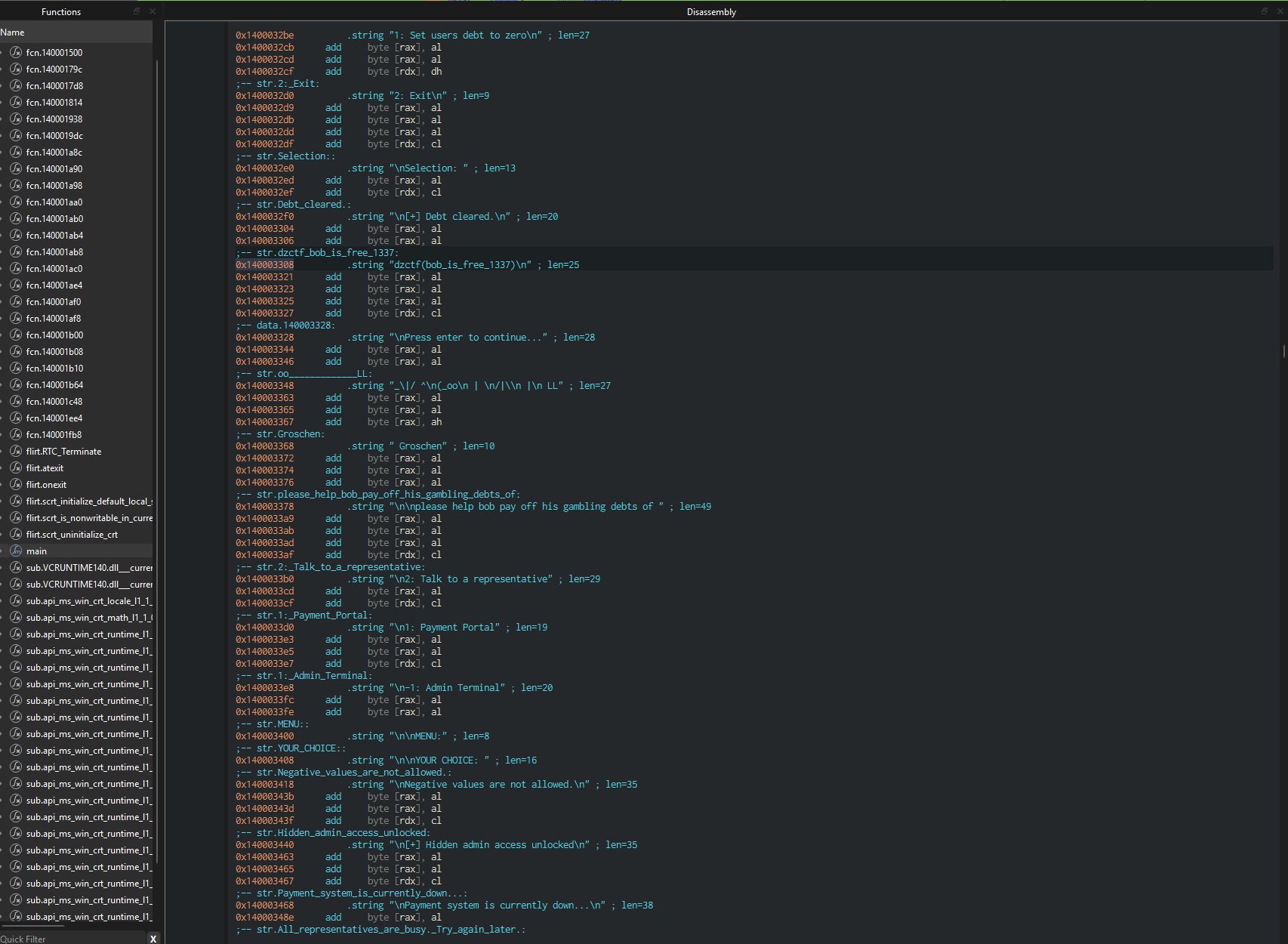
Here I found several important strings:
ADMIN TERMINAL
Debt cleared
Negative values are not allowed
Hidden admin access unlocked
dzctf{bob_is_free_1337}Finding the flag string immediately confirmed that the flag is hardcoded inside the program. The presence of ADMIN TERMINAL also suggested that there is hidden functionality not normally accessible.
At this point, I knew I needed to find where these strings are used in the code.
4. Finding the Flag Logic {#flag-logic}
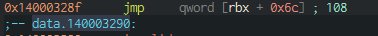
I double-clicked the flag string and opened its cross-references (X-Refs). This took me directly to the part of the code where the flag is printed.
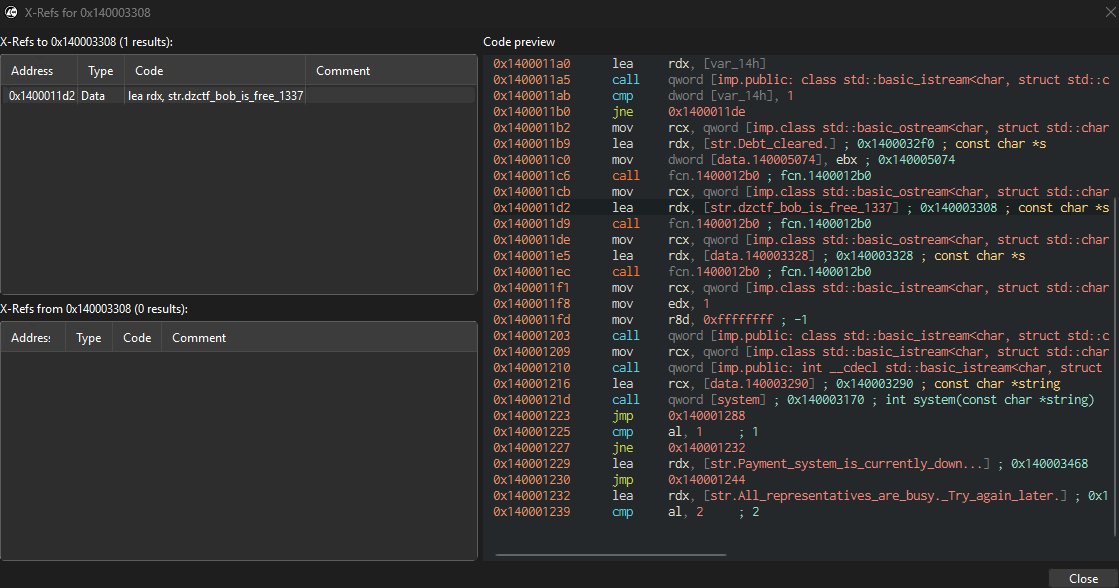
In this section, I found a comparison instruction:
cmp dword [var_14h], 1
jne 0x1400011deThis means that the program checks if a value equals 1. If the value is not 1, it jumps away. If it is 1, it continues execution and prints:
[+] Debt cleared.
dzctf{bob_is_free_1337}From this, I understood that selecting option 1 in the correct menu leads to the flag.
5. Understanding the Vulnerability {#vulnerability}
Next, I searched for the ADMIN TERMINAL string and followed its cross-references.
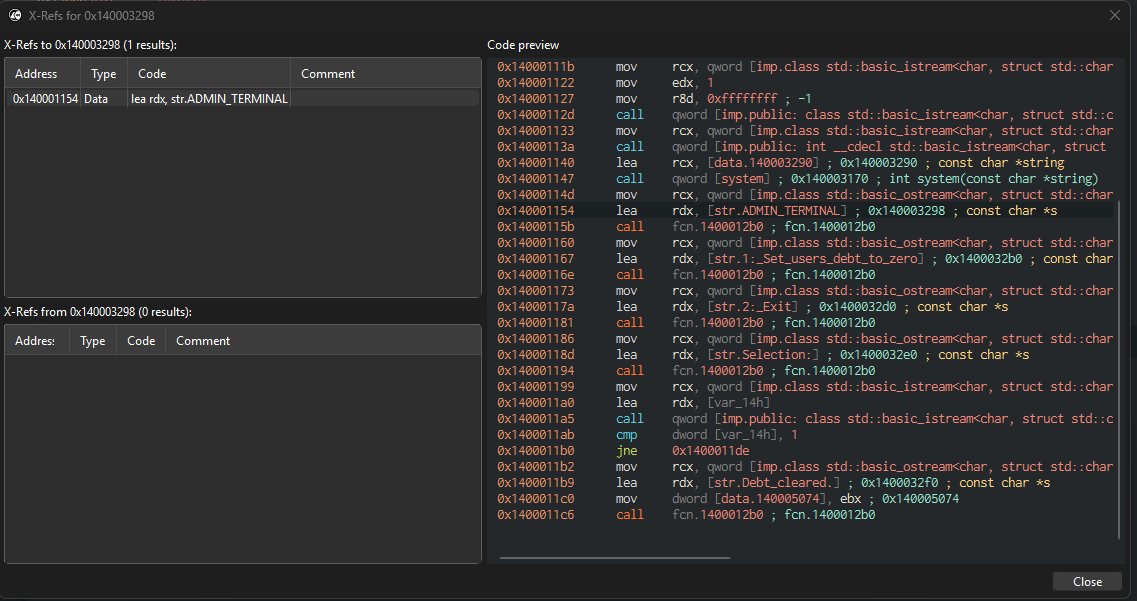
This led me to the part of the code responsible for entering the admin terminal. In that code, I found the instruction:
mov r8d, 0xffffffff ; -1This value represents -1 in signed integer form.
From this, I understood that entering -1 as input triggers the hidden admin terminal. This is a logic flaw because the program also contains a message saying Negative values are not allowed, but still allows -1 to be used for accessing hidden functionality.
Main program logic:
Input -1 → enter admin terminal
Input 1 → execute admin option → print flagAdditional Finding: Integer Truncation Bug
While analyzing further, I also noticed another interesting issue in the program. This is a classic integer truncation error.
Even though the program tries to block negative values like -1, it does not properly handle how values are stored and compared internally.
The truncation path:
Input: 255 (0xFF in hex)
↓
255 is positive → passes "no negative values" check
↓
Program casts value to single byte → 0xFF
↓
0xFF in signed form = -1
↓
Admin terminal unlockedThis confirms that the program has inconsistent handling of integer sizes, which creates another unintended way to bypass the logic without directly entering -1.
6. Patching the Binary {#patching}
Instead of entering the correct inputs manually every time, I decided to patch the binary to bypass the checks.
I located the conditional jump instruction responsible for blocking access:
jne 0x1400011de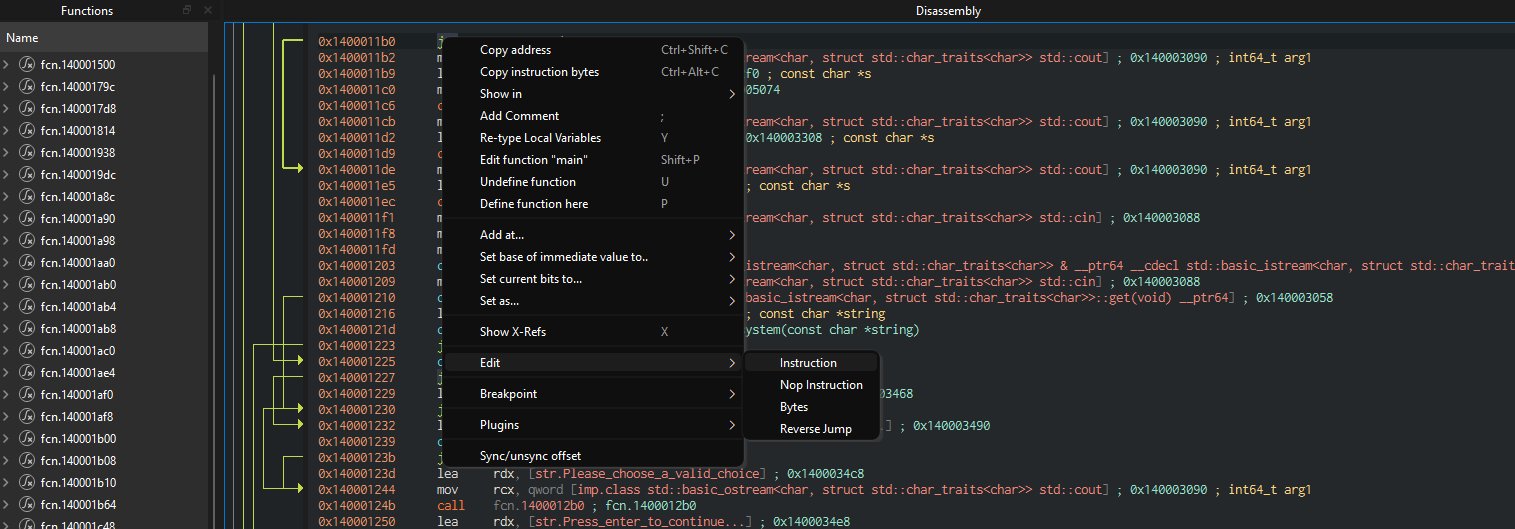
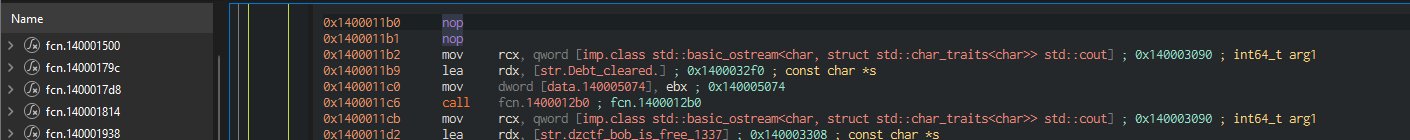
To bypass this, I replaced the instruction with NOP (No Operation) instructions. This effectively removes the condition and allows execution to always continue to the success path.
I also modified another jump instruction to ensure that the program always follows the correct execution path into the admin terminal.
Before patch: After patch:
────────────────────── ──────────────────────
cmp [var_14h], 1 cmp [var_14h], 1
jne 0x1400011de → nop
... nop
; always continues to flagBy doing this, I removed the need for specific inputs and forced the program to always reach the flag.
7. Final Result {#result}
After applying the patches, I saved the modified executable and ran it again.
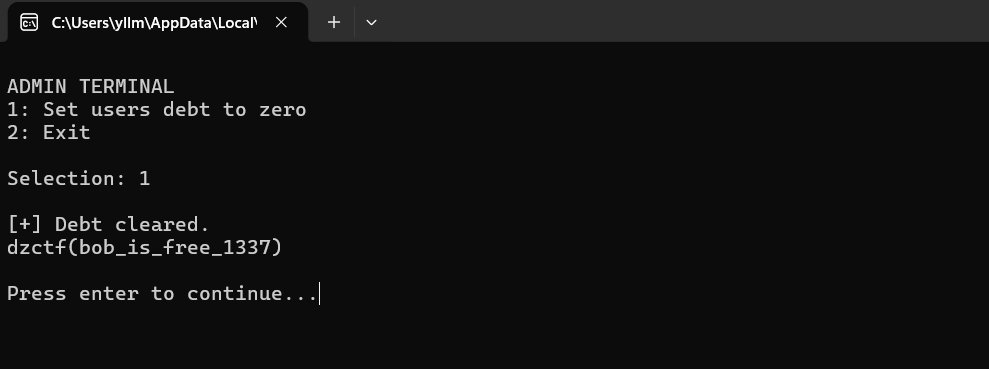
The program now directly enters the admin terminal and allows access to the flag without needing to exploit the logic manually.
ADMIN TERMINAL
1: Set users debt to zero
2: Exit
Selection: 1
[+] Debt cleared.
dzctf{bob_is_free_1337}
Press enter to continue...This confirms that the patch was successful and the program logic was fully bypassed.
8. Conclusion {#conclusion}
In this task, I successfully analyzed and modified a crackme binary using Cutter.
I started by analyzing the structure and strings, then followed cross-references to understand how the program works. I identified a logic flaw involving the use of -1 to access hidden functionality. Additionally, I discovered an integer truncation vulnerability that allows bypassing the check using the value 255.
Finally, I patched the binary to bypass conditional checks and force execution to reach the flag.
Key findings summary:
Logic flaw → -1 bypasses "no negative values" restriction
Integer truncation → 255 (0xFF) truncates to -1 at byte level
Patch applied → jne replaced with NOP → check removed entirely
Flag → dzctf{bob_is_free_1337}This task demonstrated how reverse engineering can be used to understand program behavior and how small mistakes in handling data types can lead to security vulnerabilities.
Flag: dzctf{bob_is_free_1337}